What is a Networking Computer? You must have heard it earlier, but never got a chance to learn about it. Today, I will enlighten you about it in brief. The computer network is very praiseworthy. If not for the discovery of it, you could not be reading this article (using the Internet) and I could not be writing it (I write on the computer and it is connected to my router and the router is connected to the Internet). There is no doubt that computer networks are very complex when you look at the details. But, the concept of networking by connecting computers to each other is a very simple matter. So, let’s get to know everything in detail.
What is Computer Networking?

Simply, the existence of a computer network or networking is where multiple computers are connected to each other. Moreover, it helps to share data and hardware resources. Your single computer machine is already a very powerful device. But it is possible to get more out of your machine by adding more computers or hardware (such as modems, printers, scanners, routers, etc.). The connection of computers on computer networks takes place via wires, fiber optic cables, or wireless technology. All these so that different devices (nodes) can talk to each other. We use computer networks at different times according to human needs.
Types of Computer networking
As I said before, computer networking or networking is not an easy thing, nor it is only a single type. It is mostly a complex process. Suppose, I am currently using a laptop and my laptop is connected to a home router. Also, my laptop is equipped with printers, external hard drives, and other small devices, and you can compare my current situation with PAN or Personal Area Network (Personal Area Network). Again, it can be called a single-person network.
Study smarter with ElectricPal
Built for electricians, apprentices, and electrical engineer who want faster practice and better exam prep.
Available for Android and iPhone.
But, if I give an example of an office. In an office, there is the connection of some computers together, connection of multiple printers, scanners together. In the end, the internet connection is shared with everyone. Then it will be what we know as LAN or Local Area Network. But, LANs can be much larger. It just does not confines to office or school computers or hardware. The connection of computers in an area or computers in a country or the world can be together. Again, such a huge networking system is called WAN or Wide Area Network (Wide Area Network). In fact, the Internet is the WAN that keeps computers all over the world connected.
Protocol
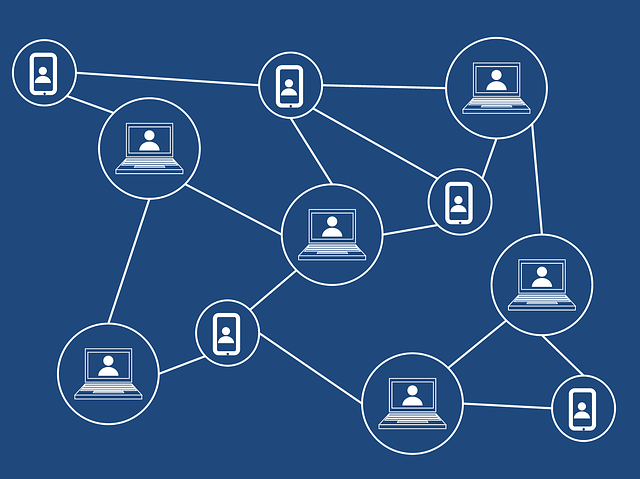
Block Chain Topology
Computers always follow the logic. Again, where there is logic there are specific rules. Computer networks can be compared to an army. Just as all the members of the army follow the rules of that team, so all the computers in the network follow the rules of that network. Speaking of LANs, for example, every node connected to a LAN (computer or other devices such as a printer, scanner) must be connected in a simple pattern called network topology. If you want you can connect the computers by drawing long lines. Here, the line from one computer to another computer, from one to another will work. Again, the machines can be connected in Star shape. Otherwise, there can be a connection of the machines by making a connection loop with the help of drawing a ring.
Moreover, the computers in the network follow the same rules and talk to each other, this is what we know as protocol. By connecting to the same line, the devices both exchange and transmit data at the same time. So if the protocol does not work, confusion will occur. As a result, it will not be possible to establish a relationship with each other.
Permission and security

Permission and security is a vital thing in a networking computer. Because, if there is the connection of any of the networking computers to your network, it does not mean that it will obey any of your commands. If you want to get any information from your other computer or use any resource, you must have its permission. For example, the Internet, where there are hundreds of websites on the server. Additionally, you can access their pages whenever you want. But, that doesn’t mean you can access every single file from the webserver. Just like I can’t access your personal files, you can’t access mine either. However, if you give permission to anybody or any networking computer, he will be able to access it.
Most connections of personal computers to the Internet only provide outgoing connections. So that they can link to another computer but block incoming connections completely. Servers keep incoming connections open subject to special software and specific permissions. No one can access that computer if the incoming connection is turned off. As a result, the data on that computer cannot be read, and the read request is ignored. If hackers want to gain access to a computer, they must gain access to that computer’s incoming connection. Firewalls can be used to protect your computer on the network. It is possible to monitor incoming traffic and outgoing traffic.
How is the network formed?
To create a computer network or networking, it is basically necessary to connect the nodes to a link. Today, for the purpose of Office and Home, this method has become a popular means of connecting devices to the network through wireless technology. But, it is still used in many offices or large networks. Because wire or fiber optic cable is much faster and more secure than wireless technology.
Is it necessary to connect your computer to another computer network first?
Each node in the network must have a special circuit, called a network card or network interface card, or NIC. Network cards are built-in on today’s new computers or laptops. But if your computer is old, you need to insert a separate network card so that it can be connected to other computers on the network. Each network card has a unique code number so that the card can be identified separately and this number is called MAC or Media Access Control.
The Process in-depth
You can compare a MAC address with a phone number. Just like we type a message to send an SMS to a number and send it to that number, a computer on the network sends a message to another computer if it wants to send its MAC address. Moreover, it is possible to ensure that any device on the network has permission to access any file through Mac. Suppose, I have a Mac White List of a specific device on the router, then only that device can be connected to my network. Macs will be checked when other devices want to connect and no connection will be provided if they do not match. This will prevent hackers or networks from unfamiliar devices from connecting.
Moreover, the bigger the networking computer system, the bigger the line you will need. If you want to create a network via wireless and if the network is large, you need to use a repeater or signal booster. You can use them to boost the signal. Here, you will also need switches, hubs, routers, etc.
Now, I believe, you know what a networking computer is and how computer networks keep computers connected to each other. There were many more topics to discuss but they are very complex issues. I will try to discuss them easily in a separate post. If you have any questions about today’s post, you can let me know by commenting below, I will try to give the correct answer.
Check More Articles:
- Common Misconceptions about Electricity and its solution
- What does mAh mean in a battery? Mystery about mAh marked in a battery
- Direction of current flow and electron flow | Why are they opposite to each other?
Ready to pass your exam?
Join thousands of electricians and apprentices using ElectricPal to study smarter and score higher.
Free to download · Available for Android and iPhone

